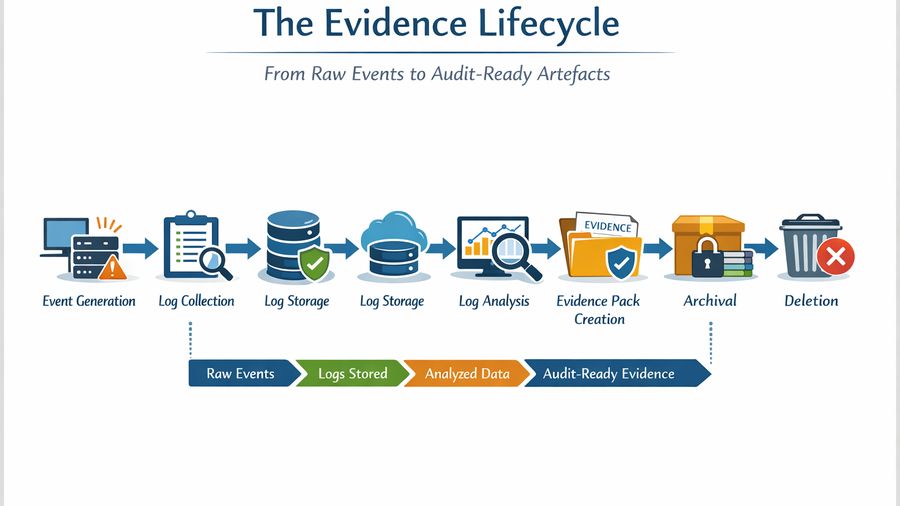
Log Retention, Deletion, and Audit Trails: Building an Evidence Program
A business-style piece for technical evaluators that explains log retention, deletion, and audit trails— building an evidence program and turns policy
13 results
A business-style piece for technical evaluators that explains log retention, deletion, and audit trails— building an evidence program and turns policy
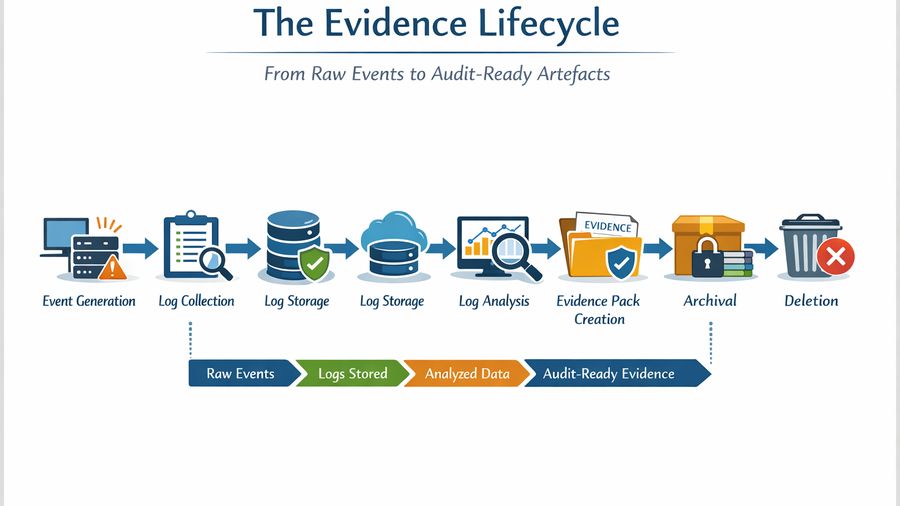
A business-style technical guide for technical evaluators that covers building a consent-aware api, implementation details, and the controls needed for
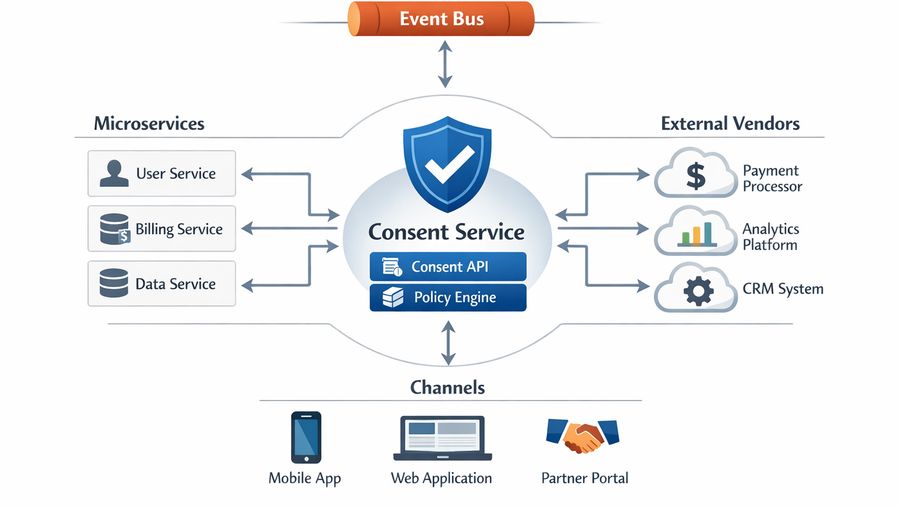
A business-style technical guide for technical evaluators that covers reference architecture— from consent banner to consent ledger, implementation details, and
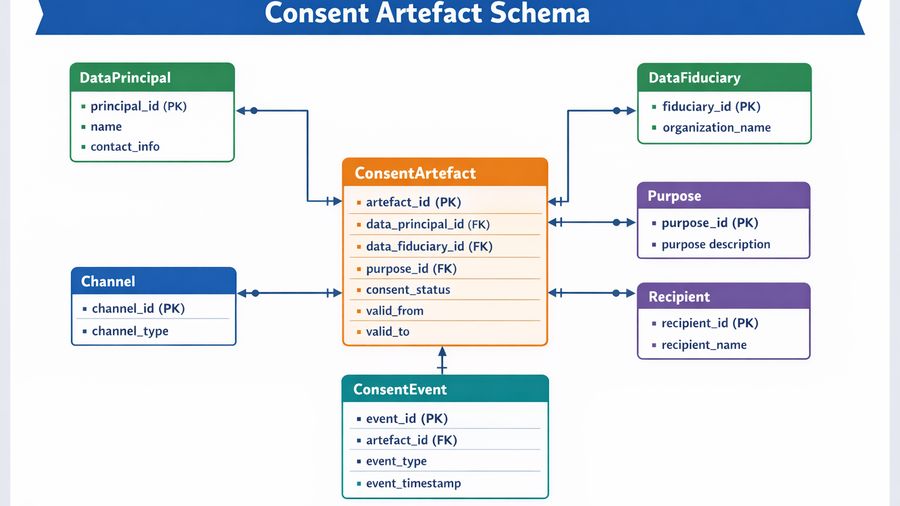
A business-style technical guide for technical evaluators that covers database schema design for consent artifacts and purpose metadata, implementation details,
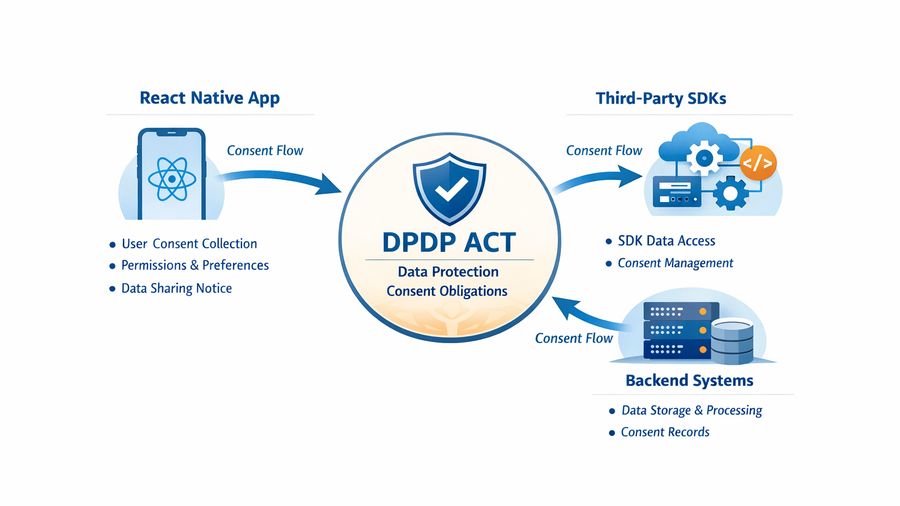
A business-style technical guide for technical evaluators that covers react native sdk guide for consent capture, implementation details, and the controls
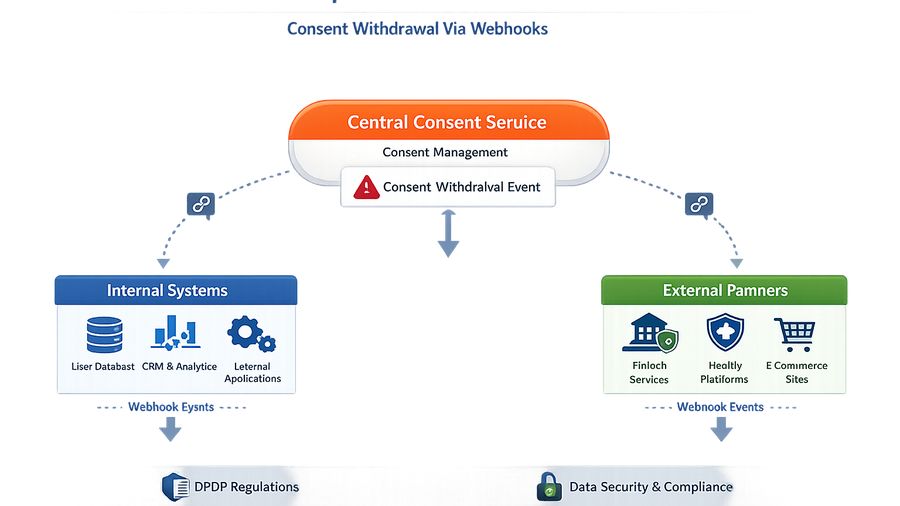
A business-style technical guide for technical evaluators that covers webhooks for consent withdrawal and downstream sync, implementation details, and the
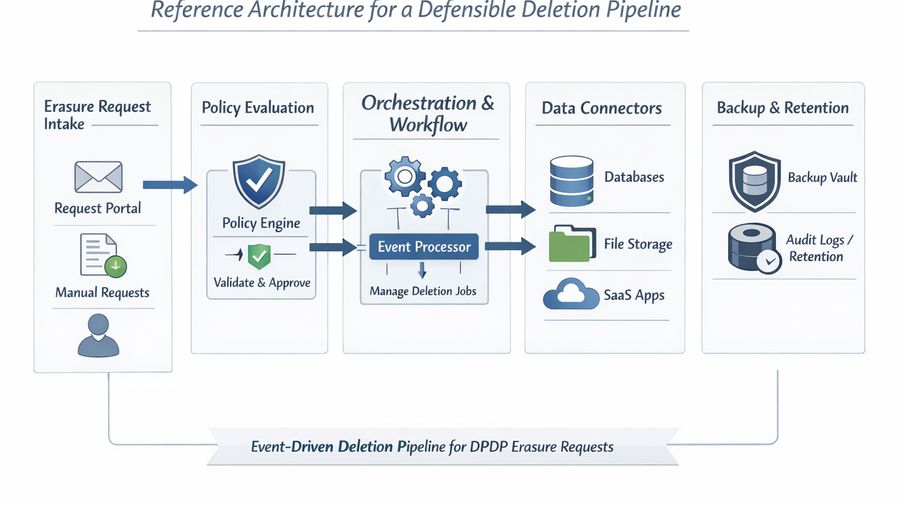
A business-style technical guide for technical evaluators that covers deletion pipelines— how to operationalize erasure requests, implementation details, and
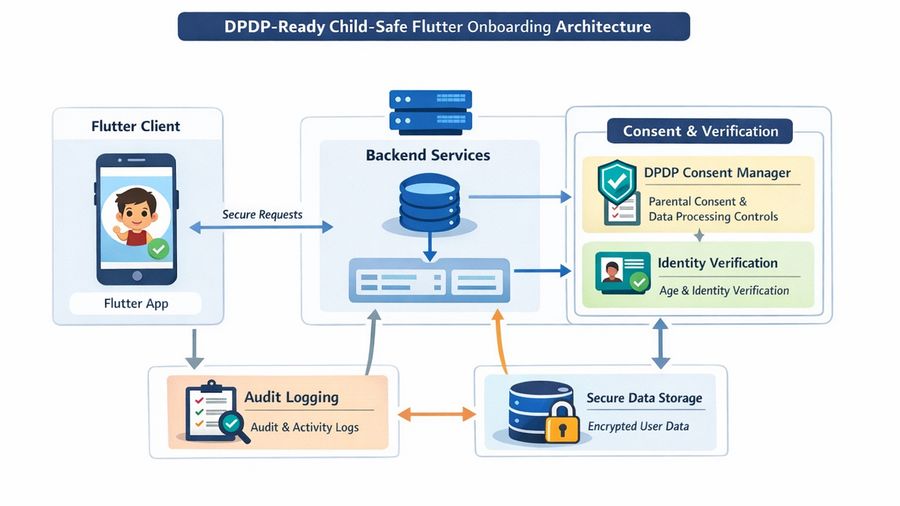
A business-style technical guide for technical evaluators that covers flutter guide for child-safe onboarding, implementation details, and the controls needed
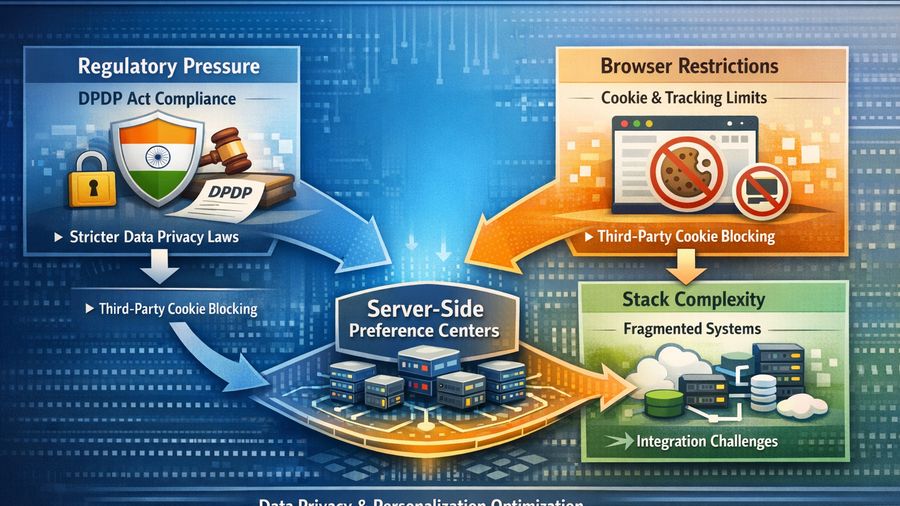
A business-style technical guide for technical evaluators that covers server-side preference centers— architecture patterns, implementation details, and the
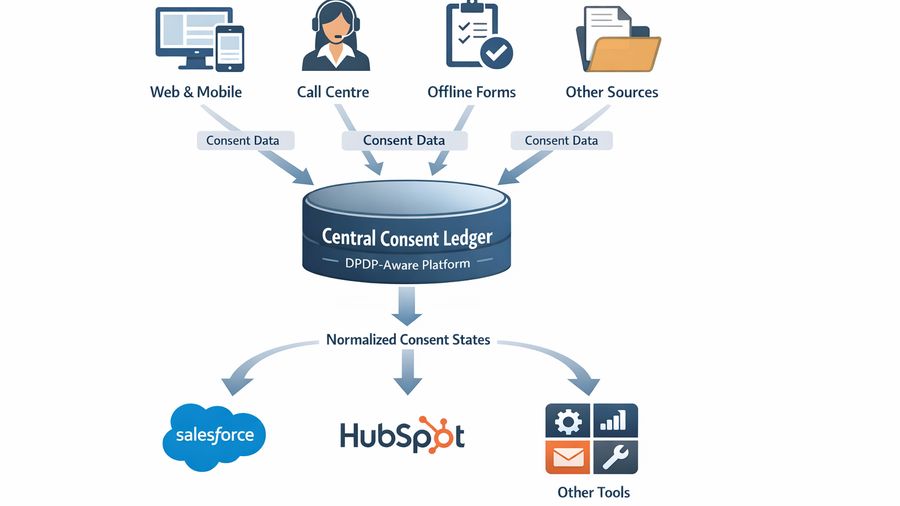
A business-style technical guide for technical evaluators that covers how to sync consent states into salesforce and hubspot, implementation details, and the

A business-style technical guide for technical evaluators that covers building a consent event taxonomy for analytics teams, implementation details, and the
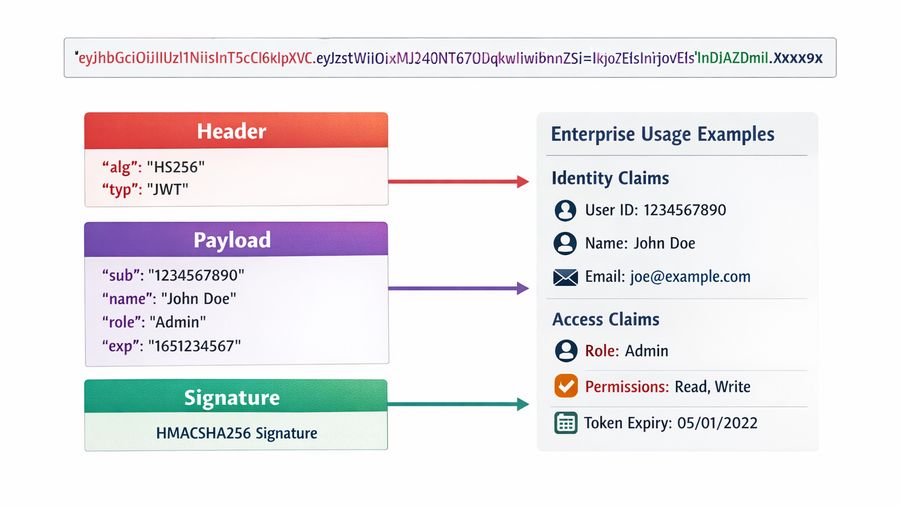
A business-style technical guide for technical evaluators that covers consent token vs jwt— designing permission-aware systems, implementation details, and the
Here to help
Share your details and the team can take it forward from here.